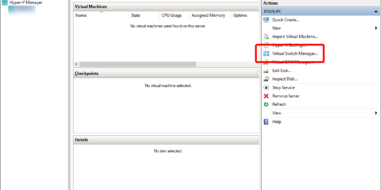
I can’t remember what triggered it, but every time I tried to start Ubuntu in Windows 10, I got the following error: I uninstalled and reinstalled Ubuntu, WSL2, ran sfc /scannow, and did everything I could to fix it. Then in a thread somebody mentioned that creating a new Virtual Switch in Hyper-V Manager solved …
Home
Quicken Won’t Start on Windows 10 after Update? We’ve got the fix!
Today’s Tale of Tremendous Troubleshooting comes from my customer Ted, who called me this week. His W10 (Windows 10) computer stopped being able to open Quicken after a Windows Update a couple of months back. He spent a lot of time with Quicken/Intuit technical support and they told him that the .NET Framework was damaged …